 |
OPTIGA™ Trust M
Host Library Documentation
|
 |
OPTIGA™ Trust M
Host Library Documentation
|
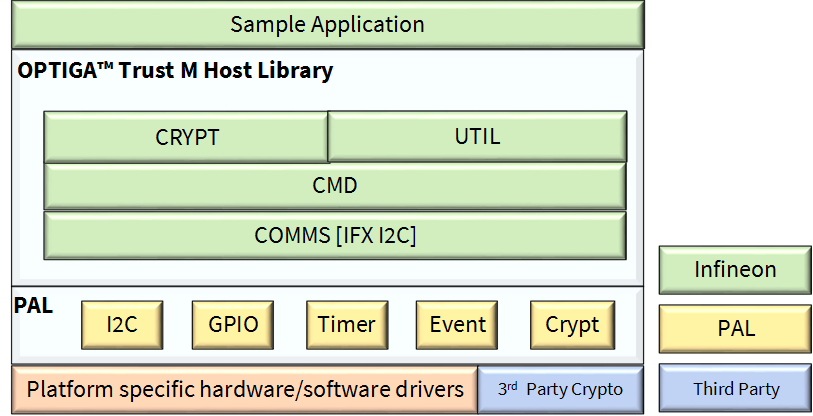
The diagram depicts the Host software stack.
| OPTIGA Features | Curves/Algorithms | Trust M V1 | Trust M V3 |
|---|---|---|---|
| ECC | ECC NIST P 256/384 | Yes | Yes |
| ECC NIST P 521 | Yes | ||
| ECC Brain pool P256/384/512 r1 | Yes | ||
| RSA | RSA 1024/2048 | Yes | Yes |
| Key Derivation | TLS v1.2 PRF SHA 256 | Yes | Yes |
| TLS v1.2 PRF SHA 384/512 | Yes | ||
| HKDF SHA-256/384/512 | Yes | ||
| AES | AES-128/192/256(ECB, CBC, CBC-MAC, CMAC) | Yes | |
| Random Generation | TRNG, DRNG, Pre-Master secret for RSA | Yes | Yes |
| HMAC | HMAC with SHA256/384/512 | Yes | |
| Hash | SHA 256 | Yes | Yes |
| Protected Data Update (Integrity) | ECC NIST P256/384, RSA 1024/2048 | Yes | Yes |
| ECC NIST P521, ECC Brain pool P256/384/512 r1 | Yes | ||
| Protected Data/Key/Metadata Update (Integrity and-or Confidentiality) | ECC NIST P256/384/521, RSA 1024/2048 | Yes | |
| ECC Brain pool P256/384/512 r1 | Yes |
OPTIGA Host Libraries:
The OPTIGA host libraries constitutes of multiple layers which provides the following functionalities.
OPTIGA Crypt:
Provides APIs to perform the following usecases using OPTIGA security chip:
OPTIGA Util:
Provides APIs to perform the following usecases with OPTIGA security chip:
OPTIGA Cmd:
Provides internal functions to form APDU commands based on user inputs, send it to OPTIGA security chip and returns the required response to the service layer(optiga_util and optiga_crypt).
The command library support APDU for the following:
OPTIGA Comms:
This layer provides the interface to communicate with OPTIGA using Infineon I2C protocol.
PAL (Platform Abstraction layer):
Platform abstraction layer for platform low level drivers like I2C, Timer, GPIO, socket and other platform dependencies. This eases the migration/porting to a different platform.
Platform Layer:
Sample Application:
Demonstrates the following usecases with and without communication channel protection: